Shodan Exposes Building Automation Systems
Back on Shodan again, this time highlighting the potential risks to Building Automation Systems (BAS). When I refer to BAS, I am talking about HVAC systems, lighting controls and security cameras—the essential infrastructure that keeps buildings running smoothly in the background.
These systems often use specialised protocols to communicate. Unfortunately, many of them—potentially all of those shown on the map below—are exposed to the public internet and are therefore vulnerable to cyberattacks.
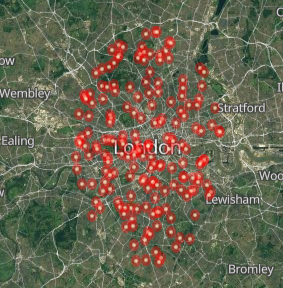
A visualisation of exposed building control protocols across the London area.
The Vulnerability Landscape
Public visibility for these systems raises serious questions. It is like leaving your apartment window wide open in a busy city: nothing might happen, but the risk is undeniably present. The primary threats include:
- Unauthorised Access: An attacker could gain control and manipulate systems—tweaking HVAC settings in a skyscraper, disabling security cameras or impacting critical infrastructure.
- Data Exfiltration: These systems store building occupancy logs and energy consumption metrics. A breach could lead to significant privacy violations.
- Operational Disruption: Even without malicious intent, vulnerabilities can lead to malfunctions, power surges or access control failures.
Mitigating the Risks
These risks are manageable with proactive security measures:
- Network Segmentation: Isolate sensitive systems from the open internet using a separate, secure network.
- VPNs for Remote Access: Use encrypted tunnels to prevent unauthorised entry to underlying systems.
- Firewall Management: Strictly configure gatekeepers to filter and restrict incoming traffic.
- Patching: Keep specialised software up to date to address known vulnerabilities that are often overlooked.
- Strong Authentication: Implement multi-factor authentication (MFA) and robust password policies.
Conclusion
The Shodan map of London serves as a vital reminder to be vigilant about securing connected infrastructure. Cyberattacks are becoming increasingly frequent, yet many can be avoided through the application of trusted cybersecurity procedures. For businesses looking to reduce manual processes and human touchpoints -- another significant area of risk -- our workflow automation service helps replace error-prone manual steps with reliable, audited automated flows.
Is Your Building Infrastructure Exposed?
Don't wait for a disruption to secure your BAS. Use our free tools to check your public footprint or contact us for a professional audit.
Access Free Security Tools